- Leon County Schools
- Security Awareness
Technology (TIS)
Page Navigation
- Overview
- Help Desk
- Policies & Standards
- Project Management Office
- Security Awareness
- Vendor Digital Systems Status
- Instructional Technology
-
Software Help Guides
- Absence Management
- Blackboard
- ClassLink
- FileBound
- LanSchool
- Learn At Home Tools
- Leon Leads / PD
- Liquid Office
- Multi Factor Auth (2FA)
- Office Suites
- Peachjar eFlyers
- Remind
-
Schoolwires
- Schoolwires FAQ
- Teacher Web Training Pg
- Teacher Quick Links
- Sample SW Apps
- Sample Page Types
- Schoolwires Sandbox
- SharePoint 365 (Online)
- Skyward
- Unify
- VPN
- Windows 7
- Windows 8
- Staff Directory
- TIS Services Catalog
- Tech Equipment User Manuals
- Training Calendar
- Web Reports
- Cool Technologies
- Survey Variations
- Clear Your Cache
Security Awareness
-
The Internet is part of everyone’s life, every day. We use the Internet at work, home, for enjoyment, and to connect with those close to us.
However, being constantly connected brings increased risk of theft, fraud, and abuse. No country, industry, community, or individual is immune to cyber risks. As a nation, we face constant cyber threats against our critical infrastructure and economy. As individuals, cybersecurity risks can threaten our finances, identity, and privacy. Since our way of life depends on critical infrastructure and the digital technology that operates it, cybersecurity is one of our country’s most important national security priorities, and we each have a role to play—cybersecurity is a shared responsibility.
Security Policies / Procedures
Policies
- 7540.04 - Staff Network and Internet Acceptable Use and Safety
- 7542 - Access From Personally-Owned Computers and/or Other Web-Enabled Devices
- 7543 - Utilization of the District's Website and Remote Access to the District's Network
Procedures
- 7530a - Security of User Access to District Technology Resources
- 7540.02 - Website Guidelines
- 7540.05 - Proper Use of E-mail Account - Rules of Conduct
- 7540.05a - Electronic Mail
- 7540.09 - Computer Operating and Security Guidelines (Computer Use Manual)
- 7540.10 - Security of User Access to District Business Systems
- 7542 - Computer Use by Non-Employees
MFA Reset Guide
Security Awareness Videos
CyberSecurity Announcements
Ouch! Security Newsletters
-
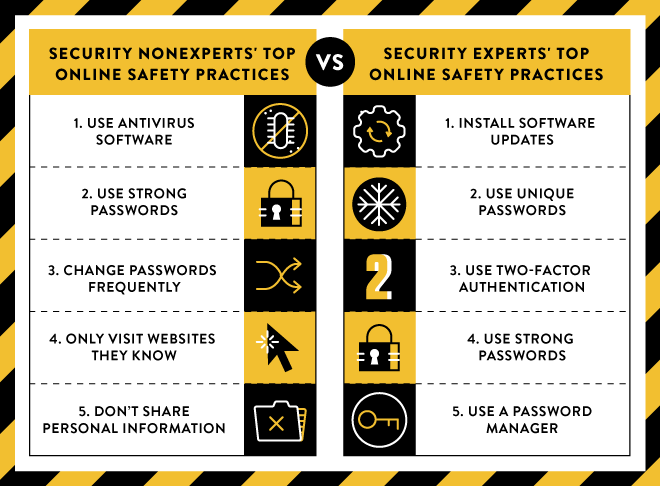
Top 5 Practices
How do you practice CyberSecurity?
Stop.Think. Connect.

-
Charles DaffinSecurity Concerns & Network / O365 2FA Resets850-487-7539
Security Resources
-
You Are A Target
This poster identifies and explains different ways cyber criminals can make money from a hacked computer. This helps ordinary computer users understand why they are a target and how they are worth money. This is an excellent resource to actively engage people in your awareness program. This poster is based on the original work of Brian Krebs.Comments (0)(1) -
Don't Get Hooked
This poster teaches people how to identify phishing and spear phishing emails. It provides an example of a common phishing email and the most common indicators that it is an attack. This poster was created as a community project based on input from numerous individuals and organizations.Comments (0)(0) -

Internet Security Guide for Kids
This presentation is for parents to present to children in grades K-5 on how they can safely use the Internet. The information here is similar to the lessons learned in Securing Your Kids, but presented in a graphical, kid-friendly manner. You are free to use this presentation for any community projects that help kids.Comments (0)(0)
Security Handouts
CyberSecurity Sites
Last Modified on July 31, 2024

